At swissns GmbH, we are committed to providing comprehensive cyber protection solutions to safeguard your valuable data and ensure business continuity. With our partnership with Acronis, a global leader in cyber protection, we offer a robust suite of services designed to defend against evolving cyber threats.
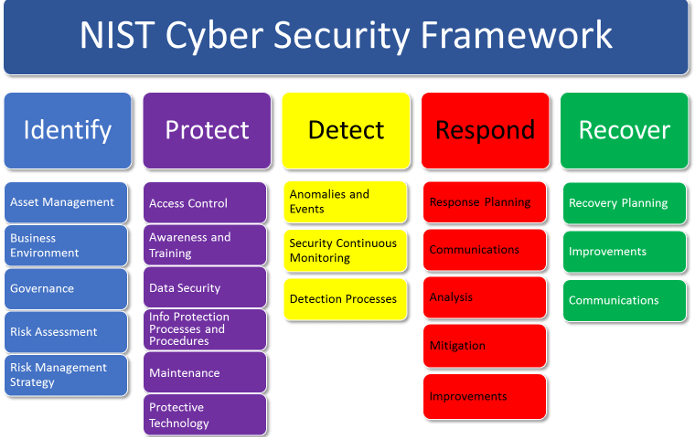
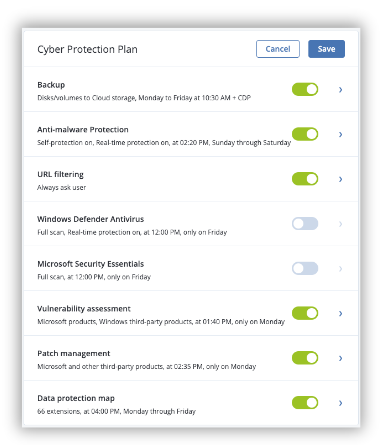
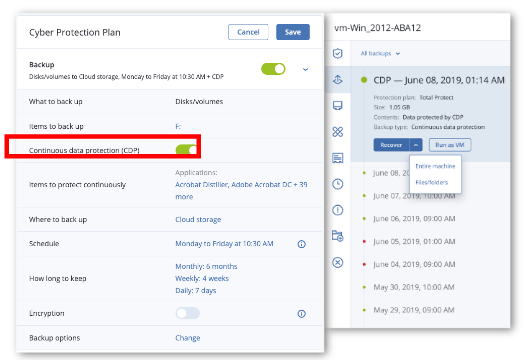
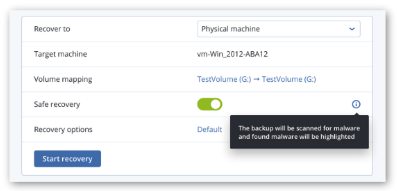
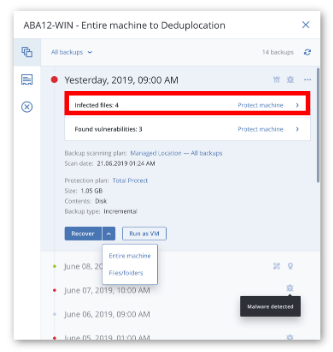
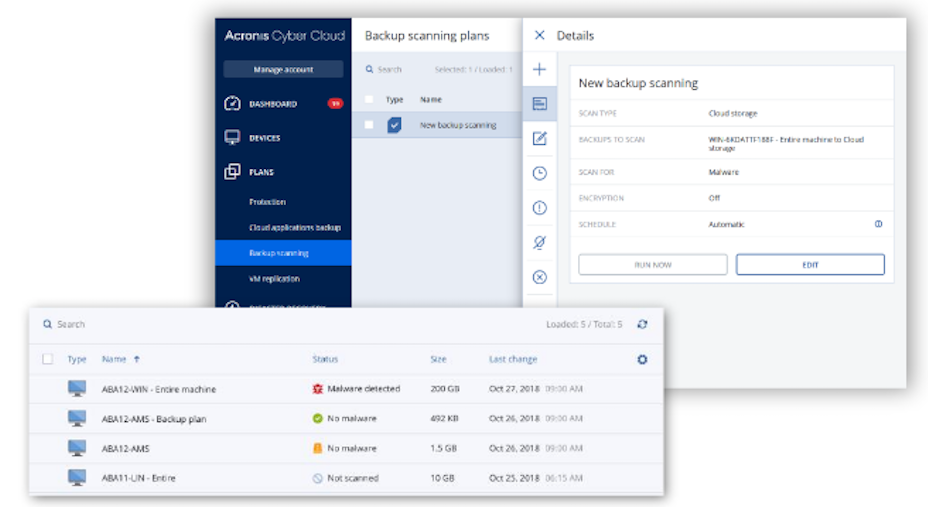
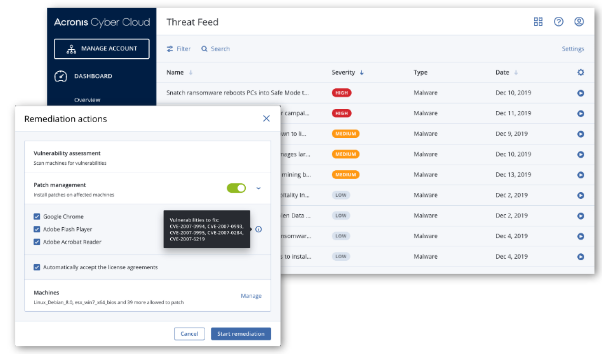
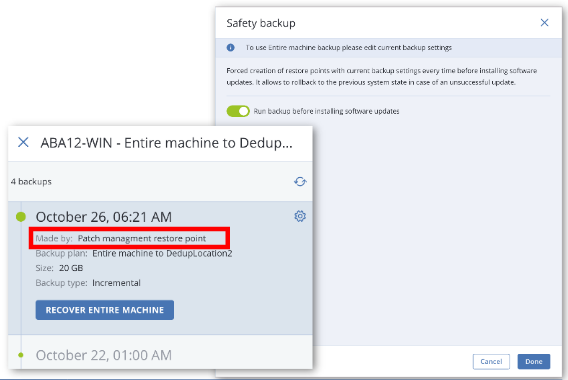
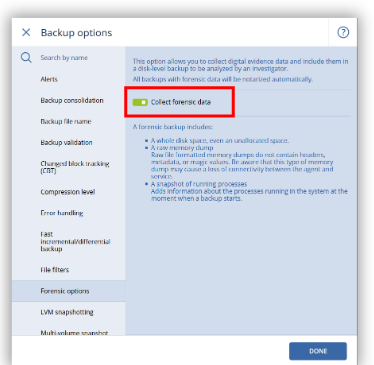
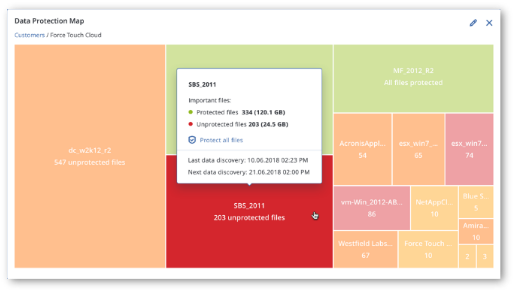
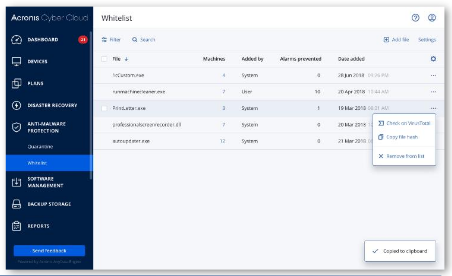
Our Acronis Cyber Protection services encompass backup and recovery, secure file sync and share, anti-malware, vulnerability assessments, and more. With advanced technologies like AI-based threat detection and blockchain-based data authentication, our solutions provide a multi-layered defense strategy that mitigates risks and strengthens your resilience against data loss, ransomware, and other cyber-attacks.